A definition of Endpoint Security
Endpoint security is the process of securing the various endpoints on a network, often defined as end-user devices such as mobile devices, laptops, and desktop PCs, although hardware such as servers in a data center are also considered endpoints. Precise definitions vary among thought leaders in the security space, but essentially, endpoint security addresses the risks presented by devices connecting to an enterprise network.
Endpoint is increasingly important
Any device, such as a smartphone, tablet, or laptop, provides an entry point for threats. Endpoint security aims to adequately secure every endpoint connecting to a network to block access attempts and other risky activity at these points of entry. As more enterprises adopt practices such as BYOD (Bring Your Own Device) and remote/mobile employees, the enterprise network security perimeter has essentially dissolved.
The need for effective endpoint security measures has increased substantially, particularly in light of the rise in mobile threats. With employees relying on mobile devices and home computers and laptops to connect to company networks and conduct business, a centralized security solution is no longer adequate for today’s ever-shifting and undefinable security perimeter. Endpoint security supplements centralized security measures with additional protection at the point of entry for many attacks as well as the point of egress for sensitive data.
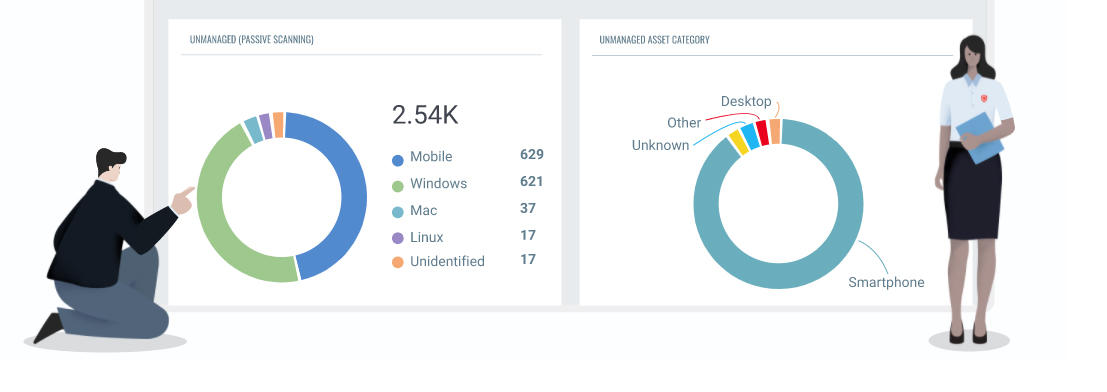
Qualys has everything you need to discover, track, and manage IT assets
For strong endpoint security, you need a complete and continuously updated inventory of these devices, such as PCs, laptops, IoT wares, peripherals and more. Qualys automatically discovers, normalizes and catalogs all your endpoint devices and captures their details— such as running services, installed software, traffic, hardware/software lifecycles, software licenses, vulnerabilities, and surfaces the information via custom dashboards, automated reports and search queries.
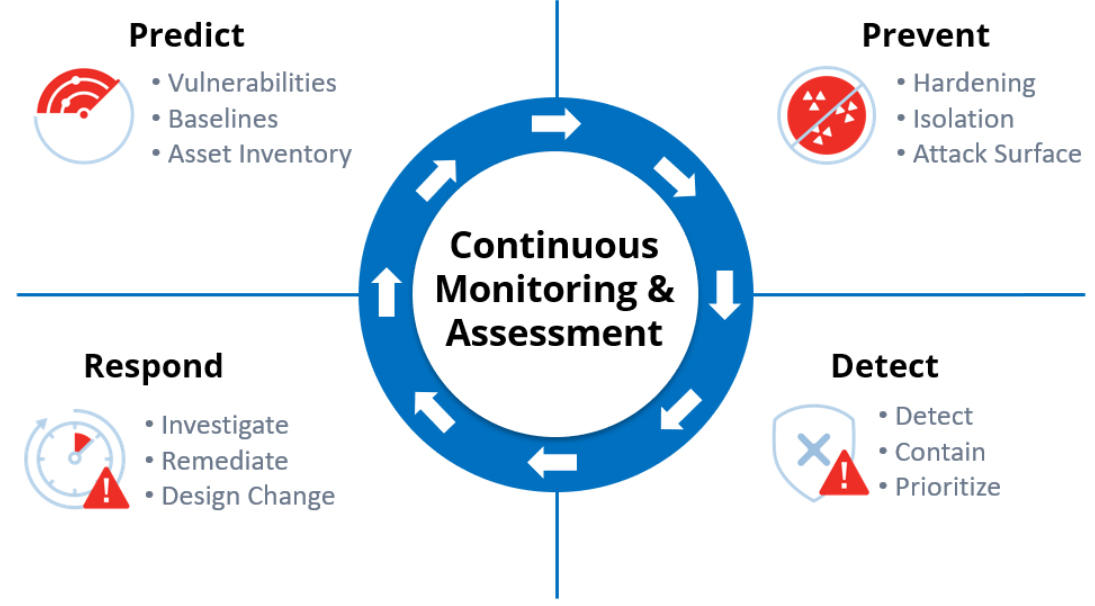
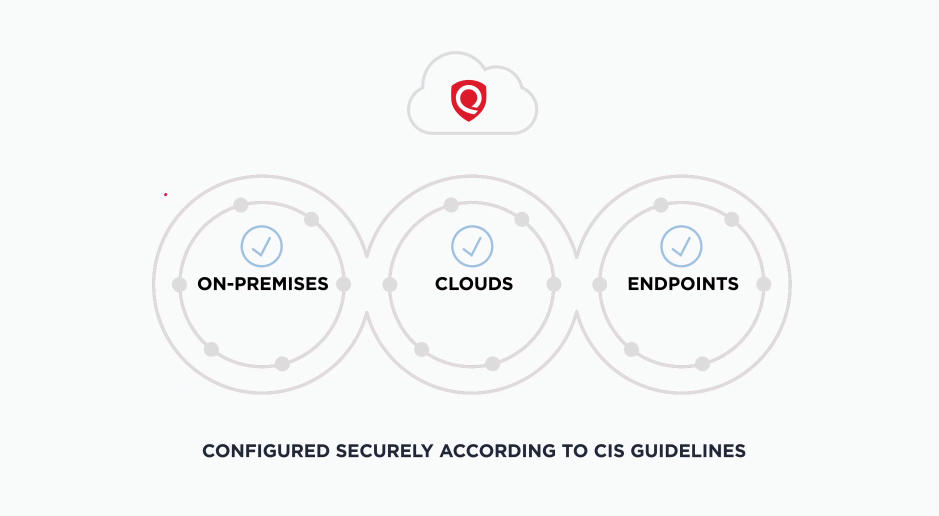
Most breaches exploit known bugs. Removing these attack vectors from your endpoint devices prevent hackers. Using both active scanning and agent-based monitoring, Qualys flags endpoints’ vulnerabilities with Six Sigma (99.99966%) accuracy. You can easily assign remediation tickets, manage exceptions, list patches, and generate different role-based reports. With Qualys, you can also address security-related configuration issues, a major source of recent breaches. Qualys automates configuration assessment of endpoint devices through out-of-the-box certified policies from the Center for Internet Security (CIS), and simplified workflows for scanning and reporting.
Comply with policies and regulations
You must ensure your endpoint devices are compliant with internal IT policies, industry mandates like PCI and government regulations like HIPAA and the EU’s GDPR. Qualys automates assessment of these assets’ security and compliance controls in order to demonstrate a repeatable and trackable process to auditors and stakeholders.
Detect malware
Qualys flags indicators of compromise pointing to malware attacks that your antivirus products may miss. With our Cloud Agents, we gather IoC data from endpoint devices, whether they’re always or intermittently connected to your network. Qualys stores, processes, indexes, and analyzes this IoC data to help with multiple use cases, including malware detection and elimination.
Endpoint Encryption and application control are critical components of endpoint security
Two key components of an effective endpoint security solution, endpoint encryption and application control are essential layers of endpoint security that prevent issues such as data leaks occurring intentionally or unintentionally through the copying or transfer of data to removable media devices. Endpoint encryption fully encrypts your enterprise data on endpoints, including laptops, mobile devices, and other endpoints, as well as in individual folders, files, and removable storage devices like CDs and USB drives.
Ask us for a personal demonstration!