Security is all about knowing who and what to trust. It is important to know when and when not to take a person at their word. The same is true of online interactions and website usage – you have to trust a website you a using, you have to know is it safe to provide your information.
Social engineering is essentially the hacking of a human, it exploits human tendency towards trust in order to manipulate into handing over specific information.
Types of Social Engineering Attacks by blog.twinstate.com
Phishing
Phishing is an example of social engineering where scam artists use to manipulate human psychology. Phishing emails use social engineering to encourage users to act without thinking things through.
Attackers count on fear and a sense of urgency. It’s common for attackers to tell users that their account is restricted or will be suspended if the targeted user does not respond to the email. Fear gets targeted users to ignore common warning signs and forget their phishing education. Even administrators and security experts fall for phishing occasionally.
Vishing
Phishing and vishing have the same goal – to obtain sensitive data from users that could be used in identity theft, monetary gain or account takeover.
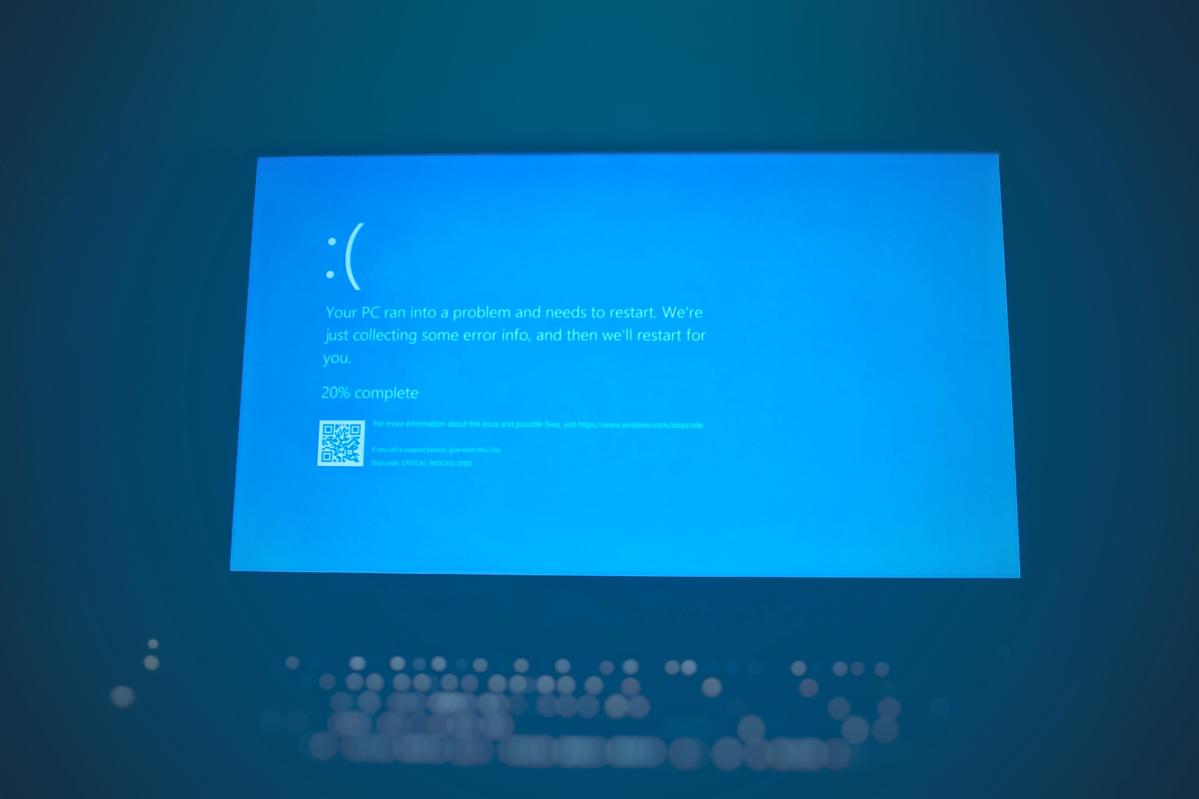
A person visits social media platform and clicks on a link. A blue screen appear with a warning message to call the toll-free number displayed to repair a serious computer problem. A pleasant technician answers the phone, more than willing to help, but for a price. After credit card information is provided to pay for the software to solve the computer problem, the con is complete, and the victim pays.
The software doesn’t work, and the helpful technician disappears. The user has become victim of a vishing.
Smishing
Smishing attack is a type of scam in which criminals send an SMS to the victim pretending to be some institution, such as a bank or a company, in order to steal personal information. The word “smishing” is a combination of the terms SMS (short for “short message services”) and “phishing”.
For example, you might get what looks like a text from a company you do business with, such as your bank, a mobile provider, or a tech service like Netflix or PayPal. It claims your account has expired or been locked on some pretext, maybe suspicious activity, and you need to provide personal information or click on a link to reactivate it. That gives the scammers means to steal your money or identity or to infect your device with malware.
Pretexting
Pretexting is often at the heart of every good social engineering attack, yet has numerous definitions, each adding to the confusion of what it actually is. For example, the Webster’s dictionary defines it as: The practice of presenting oneself as someone else in order to obtain private information.
This is close but is really only describing impersonation. Furthermore, the objective may not necessarily be private information. Various online sources define pretexting in exactly the same way as social engineering is often defined: The art of manipulating individuals into revealing sensitive information. Sciencedirect.com names pretexting as a method of inventing a scenario to convince victims to divulge information they should not divulge. Pretexting is often used against corporations that retain client data, such as banks, credit card companies, utilities, and the transportation industry. Pretexters will request information from the companies by impersonating the client, usually over the phone.
Business Email Compromise (BEC)
Business email compromise (BEC) is a type of email cyber crime scam in which an attacker targets a business to defraud the company. Business email compromise is a large and growing problem that targets organizations of all sizes across every industry around the world.
A BEC attack relies upon the ability to look like someone with power within a company or a trusted external partner. An attacker can accomplish this in a few different ways, according to Checkpoint.com
Domain Spoofing: Email address verification is not built into the email protocol (SMTP) by default. This means that an attacker can fake the display name and sender address of an email to make it look like it came from inside the company or a trusted vendor. SMTP allows the sender to define a different address to send replies to, ensuring that they receive any responses.
Lookalike Domains: Lookalike domains are designed to take advantage of characters that can be easily confused. For example, the domains company.com and cornpany.com look similar enough that they could fool someone not paying attention.
Compromised Accounts: If an attacker has access to a legitimate account, they can use it in a BEC attack. This adds a level of authenticity because the email is actually coming from a trusted address.
ALFATEC Group can protect you from all those scams. Tell us your problem.