Digital signatures are crucial to improving all sorts of business process as well as digital identity. They drive security, legal validity, and records management efficiency.
Digital signature has 3 important properties:
– It proves the owner of the private key has authorised the signature.
– The proof is undeniable and can not be repudiated.
– The signature was not modified by anyone after it was signed.
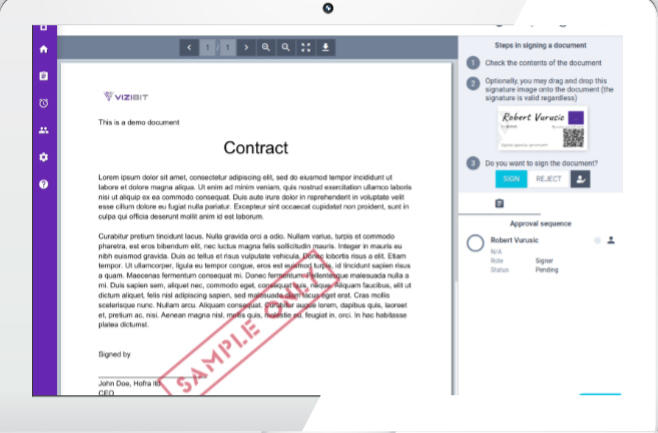
The objective of the digital signature is to ensure reliability, integrity and security. To achieve this, a Digital Signature Platform – Signator, manages and generates digital signatures which are uniquely linked to the individual who has applied it and linked to the Electronic Document to which it has been applied in such a way that any subsequent change to the Electronic Document is easily detectable.
Digital signature methodology uses PKI. Under PKI principles, each individual signing documents has their own ‘digital identity’, made up of three components:
- A digital certificate issued to that individual. An individual’s Digital Certificate contains information about their identity, about the certificate authority who issued it to them, about the Digital Certificate itself (e.g. its expiry date), and their Public Key.
- A public cipher or ‘key’ (a ‘Public Key’). The details of an individual’s Public Key are described in their Digital Certificate and can be used to verify any digital signature of that individual and make sure the Electronic Document to which it was applied has not been subsequently edited or tampered with.
- A private cipher or ‘key’ (a ‘Private Key’). When an individual digitally signs an Electronic Document, they do so using their Private Key. Each Private Key must be securely stored by the certificate authority while remaining accessible only to and under the sole control of the individual to whom it belongs.
Any digital signature can be independently validated using the signatory’s Public Key. Validation is a major advantage of digital signatures and is likely to be of great assistance in any legal dispute arising over its genuineness, authenticity or application to the Electronic Document.
This validation happens with a high assurance level:
– Authentication: Demonstrating that the digital signature is unique to, and therefore has been applied using, the signatory’s Private Key. This can be independently validated, with mathematical certainty, using the signatory’s Public Key (which forms part of the digital signature).
– Data integrity: Demonstrating that the contents of the digitally signed Electronic Document have not intentionally changed since the signatory applied their digital signature. This can be independently validated, with mathematical certainty, using the signatory’s Public Key (which forms part of the digital signature).
– Non-repudiation: Demonstrating that the signatory can be identified, and their Private Key was under their sole control when they digitally signed the Electronic Document.
If security and privacy are your main concern and uploading sensitive documents to on-line signing solutions is not an option, you can choose from our ON-PREMISES suite of solutions:
– Signator-PREMISES
Allows you to effortlessly define an automated signing workflow process. Use it to initiate digital signing between your internal users, external partners or clients. Upload your documents, define your signatories and start your signing workflow.
– Signator-eForm
Allows YOU to convert your existing PDF forms into active ones so that they can be published on YOUR web portal and accessed by your clients via browser. With a digitally signed and legally binding PDF document, you will receive its underlying data in a structured format for additional automation!
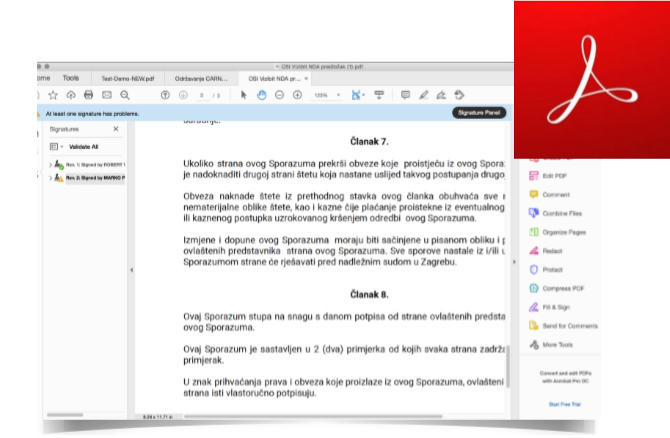
– Signator-DESKTOP
YOU can sign documents on your desktop computer so your files never leave your digital environment. We have built a FREE Adobe Acrobat reader plugin so you can quickly and easily sign documents with your digital identity.
Contact our expert for personal demonstration!