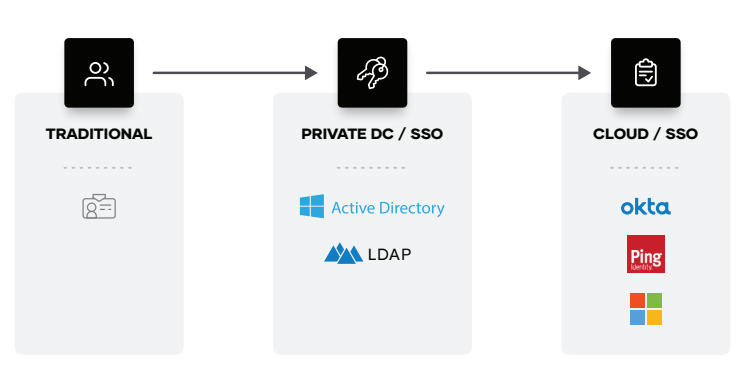
As companies move to the cloud, the measures they took to secure their private datacenters start to disappear. IP-based perimeters and access are replaced by ephemeral IP addresses and a constantly changing workforce with the need to access shared resources.
Managing access and IPs at scale becomes brittle and complex. Securing infrastructure, data, and access becomes increasingly difficult across clouds and on-premises datacenters, requiring lots of overhead and expertise. This shift requires a different approach to security, a different trust model. One that trusts nothing and authenticates and authorizes everything.
Because of the highly dynamic environment, organizations talk about a “zero trust” approach to cloud security. What does “zero trust” actually mean and what’s required for you to make it successful?
Zero Trust is a security framework requiring all users, whether in or outside the organization’s network, to be authenticated, authorized, and continuously validated for security configuration and posture before being granted or keeping access to applications and data. Zero Trust assumes that there is no traditional network edge; networks can be local, in the cloud, or a combination or hybrid with resources anywhere as well as workers in any location.
Zero Trust is a significant departure from traditional network security which followed the “trust but verify” method. The traditional approach automatically trusted users and endpoints within the organization’s perimeter, putting the organization at risk from malicious internal actors and rogue credentials, allowing unauthorized and compromised accounts wide-reaching access once inside. This model became dated (and in some cases obsolete) with the cloud migration of business transformation initiatives.
Zero Trust architecture therefore requires organizations to continuously monitor and validatethat a user and their device has the right privileges and attributes. It requires that the organization know all of their service and privileged accounts, and can establish controls about what and where they connect. One-time validation simply won’t suffice, because threats and user attributes are all subject to change.
As a result, organizations must ensure that all access requests are continuously vetted prior to allowing connection to any of your enterprise or cloud assets. That’s why enforcement of Zero Trust policies rely on real-time visibility into user credentials and attributes such as:
- user identity and type of credential (human, programmatic)
- number and privileges of each credential on each device
- normal connections for the credential and device (behavior patterns)
- endpoint hardware type and function
- geo location
- firmware versions
- authentication protocol and risk
- operating system versions and patch levels
- applications installed on endpoint
- security or incident detections including suspicious activity and attack recognition
Zero Trust is one of the most effective ways for organizations to control access to their networks, applications, and data. It combines a wide range of preventative techniques including identity verification and behavioral analysis, microsegmentation, endpoint security and least privilege controls to deter would-be attackers and limit their access in the event of a breach.
It is not enough to establish firewall rules and block by packet analysis – a compromised account that passes authentication protocols at a network perimeter device should still be evaluated for each subsequent session or endpoint it attempts to access. Having the technology to recognize normal versus anomalous behavior allows organizations to step up authentication controls and policies rather than assume connection via VPN or SWG means the connection is fully safe and trusted.
This added layer of security is critical as companies increase the number of endpoints within their network and expand their infrastructure to include cloud-based applications and servers – not to mention the explosion of service accounts on microsites and other machines hosted locally, VM, or via SaaS. These trends make it more difficult to establish, monitor and maintain secure perimeters. Furthermore, a borderless security strategy is vital for organizations with a global workforce who offer employees the ability to work remotely.
Contact us for more information about Zero Trust!